A sophisticated phishing campaign targeting Windows systems leverages multiple evasion techniques, including Python obfuscation, shellcode generation, and loading, to deploy a payload of malware.
This multi-stage attack, disguised as a customer service request, delivers malicious attachments that, once opened, install XWorm, VenomRAT, AsyncRAT, and PureHVNC, which grant attackers remote system control, posing a significant threat to any organization.
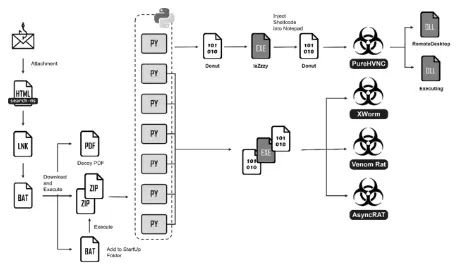
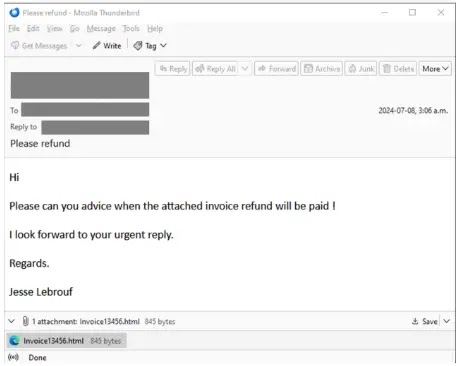
An attack begins with a phishing email containing an HTML attachment, which leverages the ‘search-ms’ protocol to execute a malicious LNK file disguised as a PDF from a remote file share.
Are you from SOC and DFIR Teams? Analyse Malware Incidents & get live Access with ANY.RUN -> Get 14 Days Free Access
The LNK file employs a command to run a batch script using ‘conhost.exe’ as a parent process, likely to evade detection by combining social engineering, file manipulation, and process injection techniques to compromise the target system.
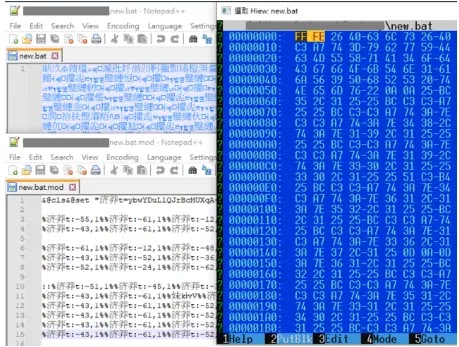
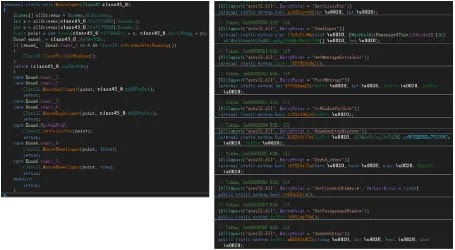
The obfuscated batch file employs character substitution and encoding manipulation to disguise its malicious intent.
After decoding, it launches a decoy PDF, downloads and extracts ZIP archives containing a Python environment and malicious scripts to the user’s Downloads folder, and executes the Python payload.
To establish persistence, it reopens the decoy PDF, downloads a second batch file to the startup folder, and extracts additional Python scripts. Finally, it cleans up unnecessary files.
A Multi-Layered Python-Based Shellcode Loader Was Analyzed.
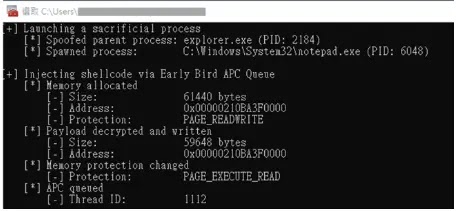
The initial stage involves obfuscated Python scripts utilizing RC4 encryption and ctypes for shellcode execution.
Subsequent stages employ a donut shellcode generator to create a first-stage payload capable of AMSI/WLDP bypass, followed by a laZzzy-based injector that disguises itself as MMC and injects shellcode into notepad.exe using Early Bird APC Queue.
The PureHVNC malware is a .NET-based RAT that leverages AES encryption and Gzip compression to obfuscate its payload.
Upon execution, it extracts configuration data, establishes communication with a C2 server, and collects system information, including sensitive data paths.
It uses PowerShell and Win32 APIs for persistence and stealth. The malware downloads and executes additional plugins from the C2 server, identified by the consistent reference to the PureHVNC library.
PluginRemoteDesktop is a malicious DLL that establishes remote desktop control over an infected system, extracts command and control (C2) information from its binary parameter and subsequently communicates with the C2 server.
It implements mouse-controlled functions leveraging specific APIs, enabling the threat actor to manipulate the victim’s system remotely.
PluginExecuting is a versatile malware module capable of executing arbitrary files, updating itself, and even uninstalling malicious components.
It operates under C2 control, receiving commands to perform actions like downloading and executing files, both locally and in memory.
By leveraging process hollowing for code injection, the malware can execute malicious payloads within existing processes.
According to FortiGuard Labs, it includes multiple IOCs, specifically six C2 domains (drvenomjh, vxsrwrm, ncmomenthv, ghdsasync, anachyyyy, and xoowill56, all on duckdns.org), one URL, and 33 file hashes.
These IOCs likely belong to a malicious actor operating a command-and-control infrastructure using multiple domains and distributing various malware payloads identified by their hashes.
Download Free Cybersecurity Planning Checklist for SME Leaders (PDF) – Free Download



