China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing
A China-aligned threat actor has set its sights on European government and diplomatic organizations since mid-2025, following…
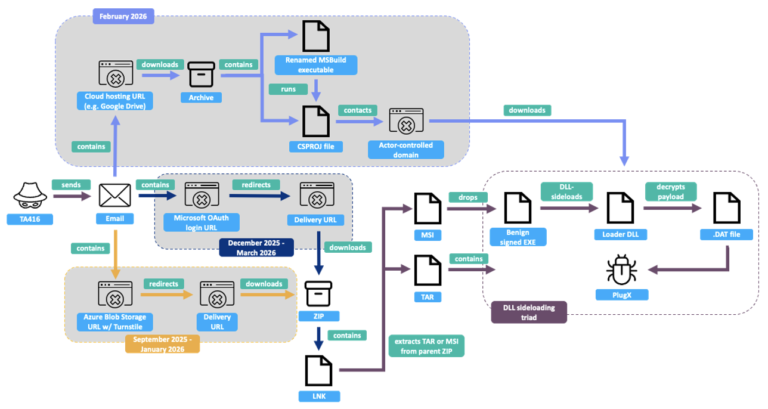
A China-aligned threat actor has set its sights on European government and diplomatic organizations since mid-2025, following…

Lloyds Banking Group to compensate 450,000 customers after app glitch exposed data. Find out how the…

Ravie LakshmananMar 28, 2026Vulnerability / Network Security A recently disclosed critical security flaw impacting Citrix NetScaler…

Ravie LakshmananMar 21, 2026Cyber Espionage / Threat Intelligence Threat actors affiliated with Russian Intelligence Services are…
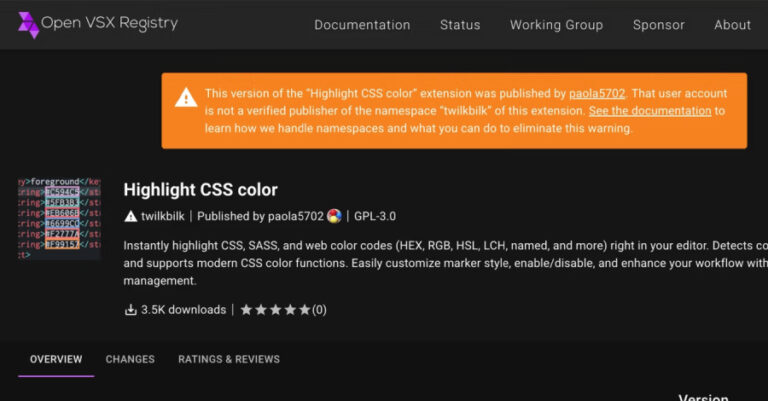
Cybersecurity researchers have flagged a new iteration of the GlassWorm campaign that they say represents a…

The Canadian telecoms giant Telus is currently picking up the pieces after a massive security breach…
A deceptive mobile phone campaign has been discovered by the research firm Acronis targeting people in…

New research has found that Google Cloud API keys, typically designated as project identifiers for billing…

A Russian-speaking, financially motivated threat actor has been observed taking advantage of commercial generative artificial intelligence…

Germany’s Federal Office for the Protection of the Constitution (aka Bundesamt für Verfassungsschutz or BfV) and…

A Farsi-speaking threat actor aligned with Iranian state interests is suspected to be behind a new…

Jan 17, 2026Ravie LakshmananArtificial Intelligence / Data Privacy OpenAI on Friday said it would start showing…

The threat actor known as Transparent Tribe has been attributed to a fresh set of attacks…

Dec 20, 2025Ravie LakshmananCybercrime / ATM Security The U.S. Department of Justice (DoJ) this week announced…

Oct 18, 2025Ravie LakshmananThreat Intelligence / Cybercrime Cybersecurity researchers have shed light on a new campaign…

Sep 27, 2025Ravie LakshmananMalware / Network Security Telecommunications and manufacturing sectors in Central and South Asian…
🚀 This game-changing capability helps security teams gain deep visibility into who inside your AWS org…

A patient’s death has been officially connected to a cyber attack carried out by the Qilin…